BOOST PRODUCTIVITY
If you are considering to use Netsparker web Application Security Scanner in a formal penetration testing environment, chances are you need it to support automation, collaboration and integration with your other security tools in your SDLC. Do not worry, Netsparker handles these requirements with ease.
AUTOMATION
Netsparker offers a rich Command Line Interface (CLI), enabling you to automate web security scans and to easily integrate Netsparker into your software development lifecycle (SDLC), automated security scan programs, reporting and development systems.
SCHEDULED SCANNING
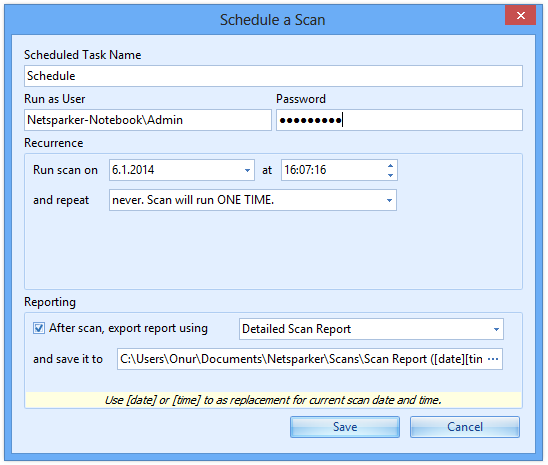
For evolving web applications that require regular and repeated web application security testing, Netsparker allows scanning to be scheduled for automatic and unattended execution.
The scheduling mechanism is very flexible, supporting individual one-time scheduled execution, as well as daily, weekly or monthly recurrence. The scheduling mechanism can also automatically generate multiple scan reports with template-based unique naming.
FULL CONTROL OF SCAN SESSIONS
Scanning a large web application can be a time-consuming process and there may be occasions when you need to interrupt the web security scan and resume it later.
Each web application security scan can be paused and resumed at a later stage. Netsparker accommodates this by allowing any scan session, even incomplete scans, to be saved to a local disk file. The file may be subsequently re-loaded at a later stage and, in the case of an incomplete session, it may be resumed.
A loaded scan session is, in every respect, equivalent to a session generated directly by scanning, allowing interrogation of its data and all forms of follow-up action, such as integrated exploitation, vulnerability re-testing and generation of reports.
PERFORMANCE-OPTIMIZED SCANNING
Security scanning a large and complex web application can be very time-consuming; sometimes a web application security scan can run for days or even weeks. Netsparker includes a number of built-in features that are designed to optimize this process, often resulting in dramatic reductions in overall scanning time, thus saving precious time.
Multi-Threading
Since Netsparker’s throughput is directly affected by network latency, it makes sense to execute multiple network requests in parallel. The thread count is user-configurable, enabling performance to be balanced against resource consumption.
Parallel Scanning
Extending the concept of multi-threading, Netsparker supports parallel scanning, whereby the attack phase is launched while the web application is still being crawled, thus reducing the overall scan time.
Configurable Coverage
When testing for a specific group of web application vulnerabilities, Netsparker may be configured to omit all other vulnerability checks via Scan Profiles, thus streamlining the attack phase.
-lw-scaled.png.png)