ADVANCED SCANNING
Behind its deceptively simple user interface, Netsparker hosts an advanced suite of scanning technologies that can probe deep into your web application, identifying security flaws and exploitable vulnerabilities that other products merely leave to chance.
AJAX/JAVASCRIPT SUPPORT
As part of its response parsing mechanism, Netsparker incorporates a JavaScript engine that can parse, execute and analyze the output of JavaScript.
This allows Netsparker to successfully crawl and interpret modern HTML5 and Web 2.0 web applications that rely on client-side scripting, including custom code execution, AJAX operations or page content that is dynamically created using well-known frameworks such as jQuery.
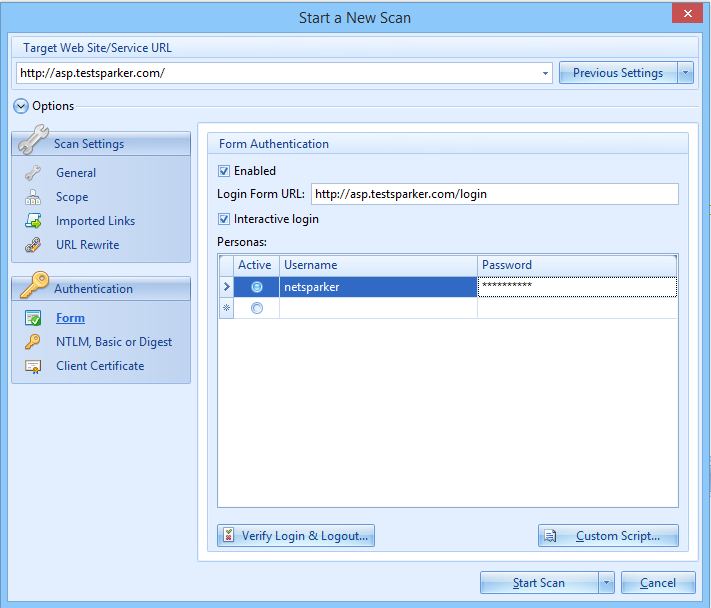
AUTHENTICATION
Nearly every web application uses authentication, so it is essential that web security scanning is able to access pages that require authentication. Netsparker addresses this need by including an authentication module that allows web application authentication credentials to be configured as part of the scan profile.
Netsparker supports the following authentication methods:
- Basic Authentication
- Form Authentication
- NTLM Authentication
- Digest Authentication
- Kerberos Authentication
ANTI-CSRF TOKEN SUPPORT
Many web applications incorporate protection mechanisms to guard against CSRF (Cross-site Request Forgery) exploitation attacks. However, most other web application security scanners are unable to successfully scan pages that use such mechanisms, rendering them ineffective at security auditing such websites.
Netsparker addresses this challenge by automatically getting a new Anti-CSRF token before carrying out requests, enabling it to offer the only complete and automated web application security scanning solution for this scenario.
AUTOMATIC DETECTION OF CUSTOM 404 ERROR PAGES
Although very popular with modern web applications, custom 404 error pages are misinterpreted by most automated security scanners and are typically reported as vulnerabilities, or can cause a scanner to report false positives.
On the other hand, Netsparker will automatically detect and properly handle custom 404 error pages to automatically detect and report vulnerabilities.
EASILY CONFIGURE URL REWRITE RULES TO SCAN PARAMETERS IN URL
Configure URL rewrite rules via a user-friendly wizard in Netsparker to scan parameters in the URL and identify any vulnerabilities they might be vulnerable to.
Unlike with other security scanners configuring URL rewrite rules in Netsparker is as easy as ABC. There is no need to know about regular expressions or have access to server configuration files. Simply launch the wizard, specify a sample URL and in the last step of the wizard simply tick the checkboxes next to the parameters names. The rest is all automated.
-lw-scaled.png.png)