Security Log Analysis and Management
Automated security log analysis and management with AlienVault USM simplifies threat detection and delivers actionable results.
Accelerate Log Analysis to Pinpoint Threats and Simplify Log Management
One of the most overlooked and underutilized tools that you can use to secure your network is log analysis. You can almost always find evidence of an attack in the logs of network devices, servers, and applications. However, if you are not performing regular analysis and effectively managing these logs, many threats may go unnoticed.
One of the core capabilities of AlienVault’s Unified Security Management (USM) platform is its ability to automatically aggregate and manage log data from its built-in detection capabilities (as well as logs produced by legacy devices in your environment). It then automatically executes advanced analysis, producing normalized events and correlating them to produce actionable intelligence, alerting you to any threats facing your environment.
With AlienVault USM, you get all of the features and functionality you expect from security log analysis and management including:
Event Correlation with Regularly Updated Threat Intelligence
- Integrated SIEM functionality automatically correlates log data from different data sources
- Regular updates to threat intelligence automatically spots the latest threats
Log Analysis Simplified with Intuitive UI and Open Plugin Architecture
- Advanced filter and search features enable fast, accurate forensic threat analysis
- Over 200 plugins included to parse logs from the most common data sources, with the ability to customize and/or create your own if needed
Multifunctional Security Log Management and Reporting
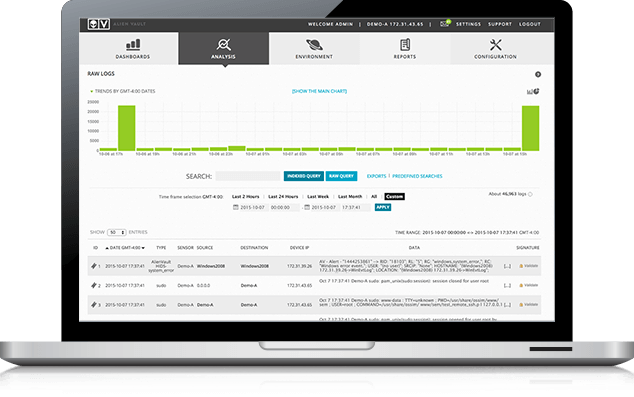
- Granular visibility into raw logs with query-based search functionality; simplifies forensic analysis compliance audits
- Digitally signed and hashed logs protect file integrity; identifies attempts of tampering
- Robust reporting engine with ability to customize and easily schedule reports
Event Correlation with Regularly
Updated Threat Intelligence
Anyone who has had to manually configure a SIEM knows that, while it can be frustrating, getting your environment’s different devices and services to send data to a collection point is not the difficult part. Most network gear, operating systems, and applications have built-in functionality to export data into the syslog format, a widely used logging standard.
The difficulty is in the actual log analysis and management of the data you’re provided with. Threat research and analysis is a full-time job in most large IT organizations so, unless you have a team investigating threats and regularly developing intelligence, you’re at a severe disadvantage.
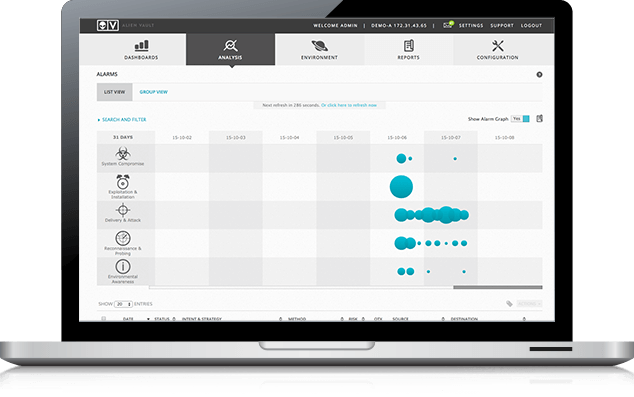
One of AlienVault USM’s core capabilities is a powerful SIEM with integrated analytical tools that normalize and correlate data to produce actionable intelligence. Rather than presenting you with only a list of events for you to search and filter through, AlienVault USM’s automated log analysis and management software can produce alarms to alert you of attacks and other security events occurring in your environment.
You receive regular updates to the advanced event correlation from our in-house team of security experts, AlienVault Labs. This group of security threat researchers is constantly on the lookout for new attack methods, traffic patterns, and malware associated with malicious activity. The regular updates to the Threat Intelligence in AlienVault USM include correlation directives, IDS signatures, vulnerability assessment data, knowledge base articles, and reports.
Multifunctional Security Log Management and Reporting
Some regulatory compliance standards require that you store logs in their raw state for a particular amount of time as well as provide for the export of this data for external analysis. Similarly, some audits (in-house or regulatory), can only be performed via queries to logs in their raw state. While some security log analysis and management software solutions can certainly ingest these raw logs, very few retain the log data in its original state, or give you the ability to export the data.
AlienVault USM features a logger as one of its main architectural components that stores log files and other data for extended periods of time. Using the built-in policy editor, you have complete control as to which logs are stored and for how long. You can also utilize policies to choose a specific set of events to go straight to the logger, bypassing the SIEM. This is helpful for non-essential events and logs that you need to retain for regulatory or even internal compliance requirements.
In addition to the raw log storage requirement, most compliance standards require that you enable controls to prevent the tampering of these logs. The AlienVault USM platform incorporates the ability to digitally sign the logs at the block or line level, ensuring that the logs you have stored have not been modified since their creation.
Another key feature of AlienVault USM that aides in log analysis and management is the reporting console. In addition to reporting on your monitored assets’ events, alarms, states of compliance, etc., you have a way to report on the activity happening on the AlienVault USM platform itself. While it sounds a bit recursive, this allows you to monitor your monitoring solution and certify compliance with your security policies and practices.
-lw-scaled.png.png)